Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
A new phishing scam has surfaced that cleverly evades inbox filters, targeting Microsoft 365 and Outlook users. Unlike traditional phishing attempts that typically involve suspicious links or obvious malware, this particular scam utilizes something most individuals trust: calendar invites. Scammers are injecting fraudulent billing alerts directly into users’ calendars, preying on their trust in calendar functionality and security.
Paul, a resident of Cape Coral, Florida, shared his unsettling experience with one such phishing attempt. He stated, “I had a very disturbing experience with a phishing attempt that almost had me hooked. I’m a Microsoft 365 subscriber and recently received the usual renewal emails. A few days later, I began receiving meeting invites indicating that my payment had failed — these appeared directly on my calendar without any action on my part. I felt anxious when I tried to delete them and discovered my only option was ‘delete and decline,’ which could trigger a response to the attacker. This was something I had never encountered before.”
Paul’s vigilance helped him avoid any interaction with the phishing event, but his story illustrates how easily such attacks can infiltrate personal and professional spaces. Here’s a detailed look at how such phishing scams function and the necessary steps to take if you encounter one.
This phishing strategy blends fraudulent calendar events, Microsoft’s branding, and social engineering tactics, making it difficult for users to discern the legitimacy of the alerts.
The scam often begins with a fake billing alert. These messages appear to come from Microsoft 365, warning recipients that their subscription renewal has either failed or been processed. In certain cases, the scam email includes a .htm attachment designed to mimic a billing portal, aiming to capture sensitive credit card details.
The tactics deployed in these scams commonly involve the inclusion of a calendar file (.ics) that places an event directly onto the user’s calendar. If the default settings in Microsoft 365 or Outlook automatically accept invites, the event appears immediately without any user action.
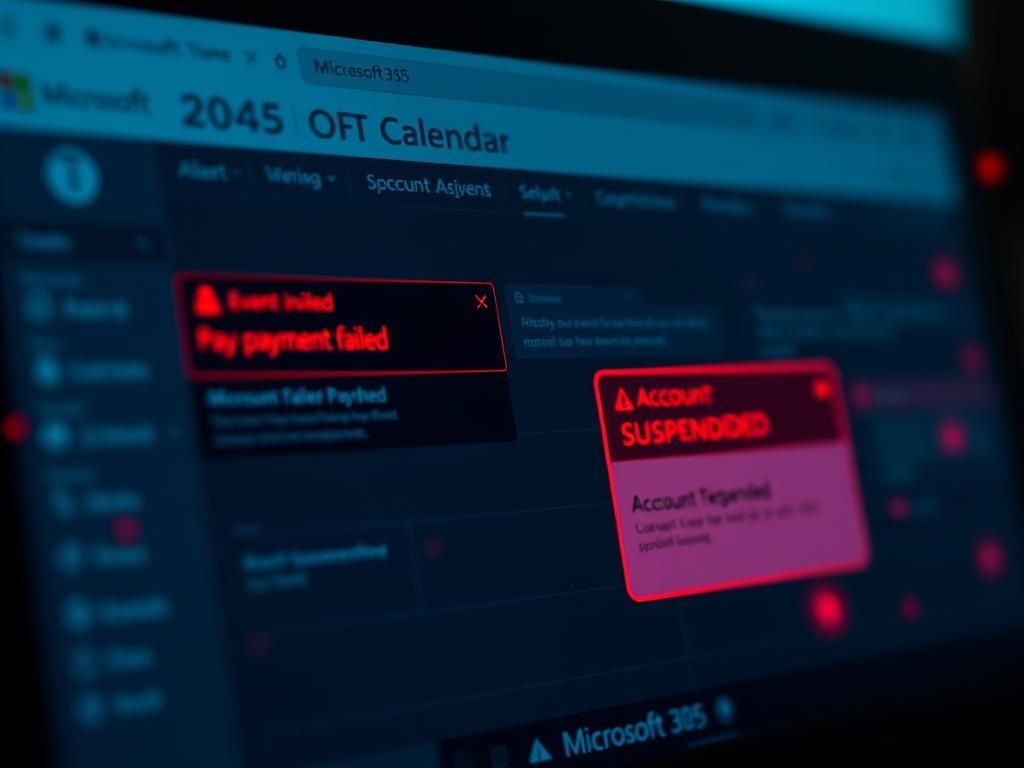
Scammers often select alarming titles like “Payment Failed” or “Account Suspended” to provoke panic. Even simply seeing such alerts can create confusion and impulsive reactions, further increasing the likelihood of interaction.
One unique aspect of this scam is that if the only removal option is “Delete and Decline,” responding in this way could confirm a user’s email and active status to the sender, which escalates the risk of further targeting.
Additionally, these deceptive invitations may originate from addresses that appear genuine, especially when sent from compromised third-party domains. Many of these messages can even pass basic security checks, complicating detection efforts for recipients.
This strategy proves effective as it exploits a vulnerability in how Microsoft 365 processes calendar invitations. Even when phishing emails are flagged or blocked, the related calendar events can still appear on the recipient’s calendar.
Traditional email security tools such as Microsoft Defender focus primarily on scanning incoming messages for harmful links and attachments. However, this attack utilizes a calendar invite that gets processed by Microsoft’s backend services, allowing the event to appear on the calendar regardless of the email security measures in place.
If users have settings that allow automatic acceptance of calendar invites, a fraudulent billing alert can appear without any clicks or interactions. This creates a sense of urgency that can make the alert feel more legitimate, particularly when it bears Microsoft’s branding.
Because these fraudulent invitations manifest within familiar environments like Microsoft 365 or Teams, they seem more credible than communications from unknown email addresses. Scammers exploit this familiarity to further deceive potential victims.
If you notice a questionable calendar event that you did not accept, it is crucial to exercise caution. Avoid any kind of interaction, including clicking links, downloading attachments, or responding to the invite. Opening the event itself is generally safe, but any reply can alert scammers and confirm your email is active.
For users operating on the latest version of Outlook, dealing with phishing invites can be tricky. Hitting