Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
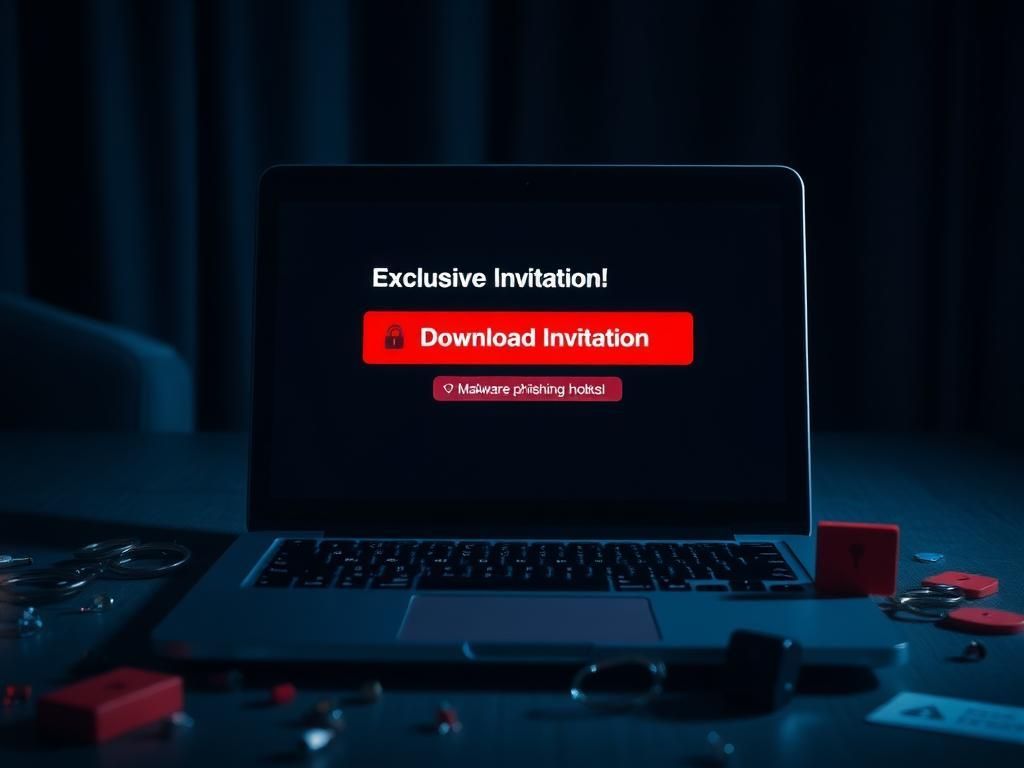
Cybercriminals are becoming increasingly sophisticated in their efforts to infiltrate our digital lives. One of their latest tactics involves sending fraudulent invitation emails that seem to originate from trusted platforms. These messages often promise you an exclusive invite or urge you to download software to view details. A careless click could lead to the installation of harmful malware on your device.
Recently, I received a particularly deceptive email. It appeared to come from a Gmail address, initially lending it an air of authenticity. However, the alarming phrase “Save the invite and install to join the list” raised red flags. No credible service should ever solicit software installation for access to an invite.
The fraudulent email I encountered looked polished and imitated well-known event platforms. Upon clicking the link, it redirected to a site that feigned hosting the invitation. Instead of displaying event information, it prompted me to download an “invitation” file.
This file likely contained malware. Once it is installed, the consequences could be dire. For instance, it could:
The suspicious link in my email directed me to a domain ending in “.ru.com.” Though it attempted to mimic a legitimate brand, the additional suffix served as a warning sign that it was authentic. Cybercriminals frequently exploit similar-looking domains to deceive users.
Identifying these warning signs can help you avoid becoming a victim:
If you notice any of these indicators, promptly close the email and delete it.
These fraudulent emails are specifically engineered to trick recipients into downloading malware, often before they realize it. To stay safe and secure, consider implementing the following strategies:
Before clicking on any “Download Invitation” button, hover your mouse over the link. Authentic invites will use the company’s official domain. Scams frequently utilize unusual endings, such as “.ru.com,” rather than standard domains like “.ru” or “.com.” This simple observation can be a lifesaver.
If you accidentally click the link, having robust antivirus protection can detect and block malware before it spreads. Think of this software as your last line of defense against unexpected threats lurking in your inbox.
To safeguard your devices against malicious links that might compromise your private information, it is crucial to utilize strong antivirus software across all devices. This software can also alert you to phishing attempts and ransomware attacks, ensuring your personal and financial data remains secure.
If you are interested in the best antivirus options available for 2025, be sure to explore what’s out there for Windows, Mac, Android, and iOS devices.
Cybercriminals often distribute these malicious emails by stealing contact lists from compromised accounts. Engaging a personal data removal service decreases the amount of personal information available online, making it more challenging for cybercriminals to target you effectively.
Though no service can entirely eliminate your data from the internet, employing a data removal service is a smart proactive step. These services can be costly, but they systematically monitor and erase your personal information across numerous websites. By limiting your online footprint, you effectively reduce the opportunity for scammers to access your information.
Check out my top recommendations for data removal services and consider obtaining a free scan to determine if your personal information is already exposed online.
Hackers preferentially target outdated systems as they are easier to exploit. Regularly updating your operating system and applications helps patch vulnerabilities, significantly strengthening your defense against potential malware attacks.
Do not simply delete suspicious invitations. Reporting them to your email provider can improve their filtering systems, benefitting both you and other users by protecting against future fraudulent emails.
Even if cybercriminals obtain your password through phishing, implementing multifactor authentication serves as an additional safeguard for your accounts. This process reinforces security, making unauthorized access nearly impossible without your phone or secondary verification code.
If malware manages to infiltrate your computer, having backups ensures you do not lose critical data. Utilize external hard drives or reliable cloud services to maintain peace of mind in the face of digital threats.
Fake invitation emails aim to catch you unawares. Cybercriminals rely on your haste, hoping you will act impulsively without weighing potential risks. Taking a moment to evaluate an unexpected email could spare you from significant security threats.
Have you encountered convincing fake invitation emails? How did you respond to them? Share your experience with us; understanding how others handle these threats could help raise awareness about this pressing issue.
Sign up for my free CyberGuy Report to receive the latest tech tips, urgent security alerts, and exclusive deals directly in your inbox. You will also gain instant access to the Ultimate Scam Survival Guide, available for free when you join.
Copyright 2025 CyberGuy.com. All rights reserved.