Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
The landscape of hacking continues to evolve, presenting new challenges for users. Cybercriminals constantly upgrade their methods, particularly with malware, to effectively scam individuals and extract personal data. As traditional strategies lose effectiveness, such as basic phishing attempts, hackers seek innovative approaches to infiltrate devices.
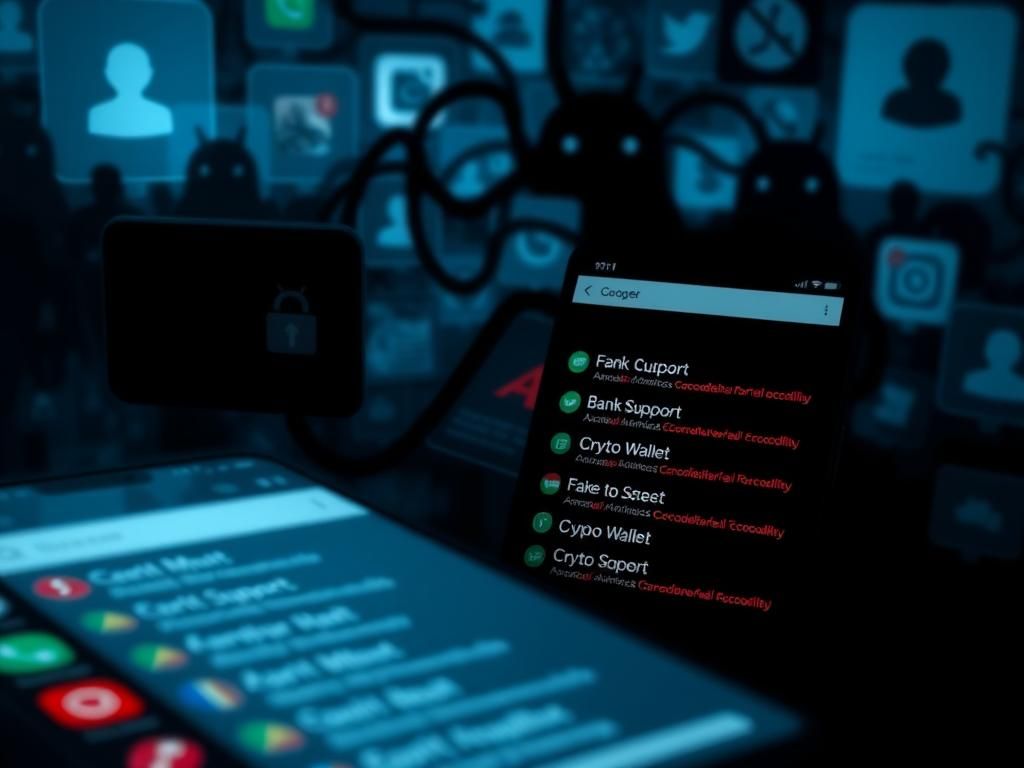
These malicious actors leverage attention-grabbing tools like social media advertisements, counterfeit banking applications, and unsuspecting system updates that appear normal at first glance. A rapidly growing threat in this realm is a malware strain named Crocodilus.
First identified in early 2025, Crocodilus is an Android banking Trojan that hijacks user contact lists to enhance the legitimacy of its scams and mask its nefarious intentions.
Crocodilus was documented by cybersecurity researchers at ThreatFabric in late March 2025. The researchers emphasized the malware’s extensive capabilities for data theft and remote device control.
This particular malware uses Facebook as a conduit for infection. It infiltrates devices via seemingly harmless advertisements, downloading itself upon user interaction. In specific instances, Crocodilus impersonated banking and e-commerce applications in Poland, enticing users with promises of free points in exchange for app downloads. These links directed unsuspecting individuals to counterfeit sites that delivered the malware. Although the advertisements were only active for a brief period, they managed to reach thousands of users, predominantly over the age of 35, a demographic more likely to have substantial bank balances.
Smaller campaigns have also emerged in the United States, where Crocodilus disguises itself as cryptocurrency wallets, mining applications, and various financial services. Often disseminated through social media ads or phishing links, these counterfeit applications prey on Android users who may not scrutinize the legitimacy of a seemingly genuine financial tool. While not yet in widespread circulation, Crocodilus’s presence in the U.S. signals a concerning global reach and the expansion of its tactics.
The Trojan has also made appearances in Spain, where it posed as a browser update targeting the majority of major Spanish banks. In Turkey, it masqueraded as an online casino application. However, the potential risks do not end there.
One major concern is Crocodilus’s capacity to insert fake contacts into users’ phones, labeling them as trusted entries like “Bank Support.” This capability can make social engineering scams more persuasive, as callers can appear legitimate. When attackers impersonate bank representatives, users may not have reason to doubt the call due to the recognizable contact name.
The latest iteration of Crocodilus presents a sophisticated seed phrase collector, especially threatening for cryptocurrency users. This malware can monitor users’ screens and utilize pattern recognition to identify and extract sensitive information such as private keys or recovery phrases, all while discreetly transmitting this stolen data to the attackers.
As Crocodilus demonstrates, future mobile threats may adopt even subtler approaches, integrating seamlessly into users’ digital lives. The malware utilizes genuine advertisements as its gateway, avoiding the need for flashy disguises to be effective. Instead, it simply needs to appear trustworthy.
This type of malware is designed for scalability. It aims to target large populations, operate across various regions, and adapt quickly. It can impersonate a banking institution, an ecommerce platform, or even conceal itself within innocuous updates. The alarming aspect is how convincingly normal it appears, making it difficult for users to anticipate malicious activity lurking within what seems benign.
The architects behind Crocodilus possess deep insights into user behavior online. They exploit this understanding to develop tools that function quietly and efficiently, likely involving a collaborative network of developers, advertisers, and distributors contributing to this effort.
Given the severity of this threat, individuals must take proactive measures to protect their personal information.
1. Avoid Downloading Apps from Ads or Unknown Sources
Crocodilus typically spreads through social media advertisements promoting seemingly legitimate banking or financial applications. Users should download apps only from trusted sources, such as the Google Play Store, ensuring they do not click on unfamiliar links.
2. Strengthen Your Cybersecurity with Antivirus Protection
Investing in quality antivirus software for your Android device can significantly mitigate risks associated with deceptive ads and malicious links. This software can help scan uploads, block harmful actions, and alert users to phishing attempts before they escalate.
3. Scrutinize App Permissions
Prior to installation, users ought to review app permissions carefully. If an app asks for access to contacts or messages without need, this should raise alarm bells. After installation, inspect system settings to verify the permissions granted. Malware like Crocodilus frequently manipulates extensive permissions to operate undetected.
4. Maintain Software Updates
Regularly updating your device is crucial in blocking known vulnerabilities. Crocodilus takes advantage of outdated systems; thus, setting devices to update automatically can help safeguard against infiltration.
5. Data Removal Monitoring Services
While indirect, monitoring services can mitigate the damage should personal information be compromised. These services track data on the dark web, alerting individuals when their credentials are at risk. Being informed can enable prompt action to prevent exploitation by scammers.
6. Activate Google Play Protect
This built-in feature scans apps for any suspicious behavior. Users should ensure that Google Play Protect is enabled on their devices and regular scans are run to enhance security.
7. Question Unfamiliar Contacts
Crocodilus’s ability to modify contact lists is particularly concerning. Users should independently verify any calls from numbers that appear to be reputable institutions. When requests for sensitive information arise, direct verification through official channels is essential.
Crocodilus represents a significant evolution in Android banking malware. It capitalizes on social media advertisements and impersonates legitimate apps to extract sensitive user data like login credentials and cryptocurrency information. Users must prioritize downloading apps from reputable sources and maintain vigilance against unusual prompts or information requests. Remaining educated on these threats safeguards digital lives against this burgeoning malware wave.
Accountability is a pressing issue as malware like Crocodilus proliferates through platforms. Readers can share their thoughts with us through our contact page.
For ongoing technology updates and security insights, subscribing to our newsletter is encouraged.