Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
ClickFix, an advanced social engineering tactic, has increasingly targeted both Windows and macOS users since early 2024. This method continues to evolve, demonstrating a notable shift in cybercriminal strategies.
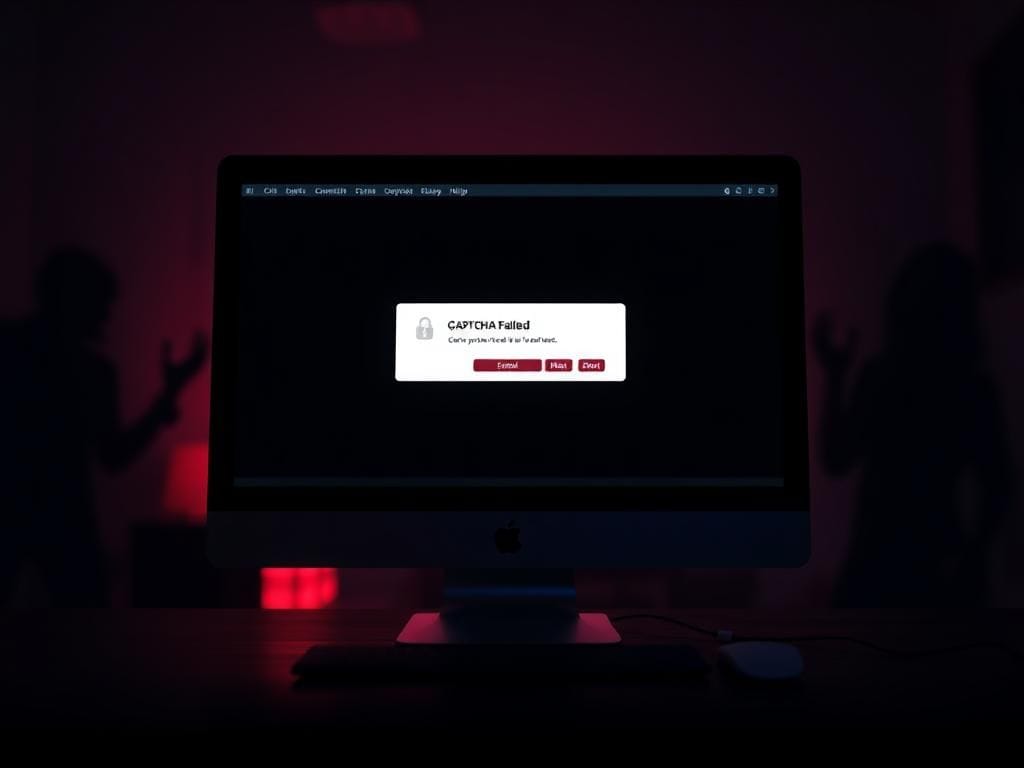
Recently, security researchers reported that attackers are utilizing fake CAPTCHA prompts to deceive Windows users into unknowingly installing malware. Now, this insidious tactic has been adapted to target macOS users.
Cybersecurity specialists from CloudSEK have unveiled a new campaign employing ClickFix to disseminate Atomic macOS Stealer (AMOS), a potent information-stealing malware that poses a significant threat to Apple systems. The campaign ingeniously uses deception to lure victims into a false sense of security.
This campaign leverages a method known as ClickFix, which entices users through fabricated online verification prompts. In this instance, the attackers have chosen to impersonate Spectrum, a major telecommunications provider in the United States. They create fraudulent domains that closely mimic Spectrum’s genuine support portals, using deceptively similar addresses such as panel spectrum net and spectrum ticket net.
Once victims unknowingly visit these counterfeit sites, they are confronted with a convincingly designed CAPTCHA box, prompting them to verify their identity. After interacting with the CAPTCHA, users receive a fake error message indicating that their verification has failed. They are then urged to click a button labeled “Alternative Verification,” which silently copies a harmful command to their clipboard.
The response that follows hinges on the user’s operating system. Specifically for macOS, the instructions guide the victim to paste and execute a command in the Terminal. This command is a disguised shell script designed not only to pilfer sensitive information but also to download malicious software.
The shell script is particularly alarming due to its use of legitimate macOS system commands, making it even more deceptive. It requests the system password, captures user credentials, and disarms security features. Following these steps, it ultimately downloads AMOS, a well-known information stealer infamous for targeting Apple devices. This malware aggressively collects sensitive information, including passwords, cryptocurrency wallet details, browser autofill data, and saved cookies.
Researchers suspect that this campaign is orchestrated by Russian-speaking hackers. Evidence supporting this theory includes comments written in Russian embedded within the malware code. Analysts have also discerned inconsistencies in the delivery infrastructure, leading them to believe the attackers did not possess sophisticated technical knowledge. For instance, some users on Linux received Windows-based commands, while Mac users were mistakenly instructed to press keys exclusive to Windows systems.
ClickFix has rapidly gained traction among cybercriminals, primarily due to its reliance on user trust and instinctive responses. In this particular instance, the attackers manipulate users into initiating the malicious installation themselves. As a result, once the users execute their actions, the system is compromised without the need for conventional exploits.
Analysts believe ClickFix has been operational since at least March 2024. Previous reports highlighted incidents where attackers employed fake error messages from major applications like Google Chrome, Microsoft Word, and OneDrive. Victims were presented with prompts that purported to offer a “fix,” echoing a sequence that copied a harmful PowerShell command to their clipboard, instructing them to run it.
By November 2024, the ClickFix method had evolved significantly. A fresh wave of attacks began targeting Google Meet users through phishing emails that masqueraded as internal meeting invitations. These emails directed victims to counterfeit Meet landing pages organized to appear as if they originated from their own companies.
To safeguard against the ongoing threat of ClickFix malware, it is essential to adopt a proactive approach. Here are six crucial security measures you should consider:
Legitimate CAPTCHA tests never require users to paste commands into Terminal. Any site requesting this action is likely to be fraudulent. If you encounter such a request, close the page immediately.
Many ClickFix assaults stem from phishing emails that imitate trusted services. Always verify the sender before clicking any links. If an email seems suspicious, navigate directly to the company’s official website instead.
Investing in reputable antivirus software across all your devices is imperative. This software can alert you to phishing attempts and ransomware threats, thereby protecting sensitive information.
When available, always enable two-factor authentication. This measure adds an additional security layer by requiring a secondary verification method, such as a code sent to your mobile device.
Regularly updating your operating system, browsers, and security solutions ensures you have the latest safeguards against vulnerabilities. Cybercriminals exploit outdated systems, so enabling automatic updates is vital.
If you suspect interaction with a malicious site or phishing email, monitor your online accounts for any unusual activity. Look for unauthorized transactions or unexpected changes in settings. If anything appears suspicious, change your passwords immediately, and consider using a password manager to help manage them securely.
Using a personal information monitoring service can provide alerts for any unauthorized use of your data. While no service guarantees complete data removal from the internet, these tools can aid in monitoring your digital footprint, offering peace of mind against potential identity theft.
Even experienced users can be deceived by tactics that masquerade as routine procedures. This attack does not solely exploit vulnerabilities in macOS; rather, it preys on user familiarity with standard verification processes. Security measures disguised as elements of typical interactions may lead individuals to unwittingly execute malicious actions. It is crucial for all Mac users to approach familiar interfaces with a heightened sense of skepticism, especially when prompted for sensitive information.
Do you believe technology companies are doing enough to combat threats like ClickFix? Share your thoughts by reaching out to us at Cyberguy.com/Contact.
For ongoing tech tips and essential security alerts, subscribe to our free CyberGuy Report Newsletter at Cyberguy.com/Newsletter.