Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Ransomware continues to pose a significant threat across various sectors, affecting numerous industries and organizations. In recent years, cybercriminals have increasingly targeted companies, leveraging ransomware to lock their data unless demands are satisfied. Instances have emerged where attackers not only seek payment but also threaten to leak stolen data, such as in the notable UnitedHealth breach, where demands soared to $22 million.
However, it’s critical to recognize that ransomware attacks are not confined to corporate environments alone. The latest FBI alert highlights a concerning trend where these attacks are extending to employees, particularly corporate executives. This shift raises alarms about the vulnerabilities present in personal and professional data security.
The FBI has issued a specific warning regarding extortion letters sent to businesses, particularly in the healthcare sector. These letters, which falsely allege to be from the notorious ransomware group BianLian, demand ransom payments in Bitcoin. The amounts range between $150,000 and $500,000, threatening to expose sensitive data if companies fail to comply with the demands.
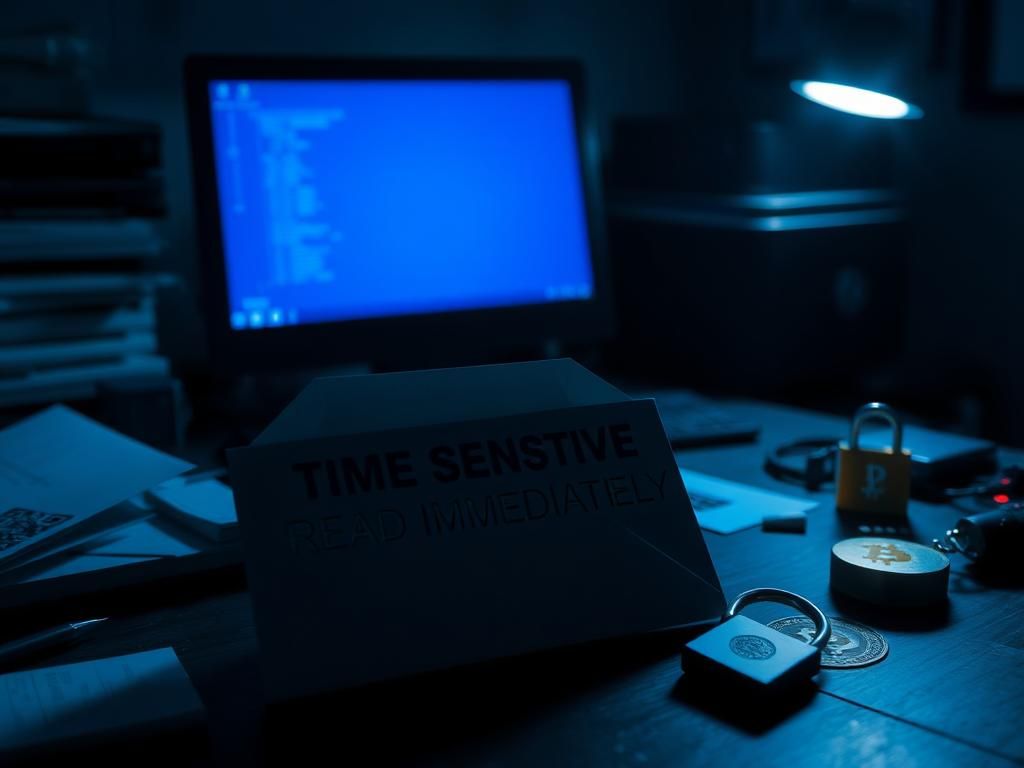
Marked with alarming phrases like ‘TIME SENSITIVE READ IMMEDIATELY,’ these letters claim that cybercriminals infiltrated organizations through social engineering tactics and siphoned off sensitive files. Despite the alarming claims, authorities have found no credible evidence supporting the existence of actual ransomware breaches within the targeted organizations. These letters appear to be template communications, displaying minimal variations while often including a QR code that directs to a Bitcoin wallet. Some letters also feature compromised passwords, likely intended to enhance the threat’s credibility.
The letters, originating from Boston and adorned with U.S. flag stamps, starkly differ in tone from verified communications known to come from the BianLian group. Authorities and cybersecurity experts believe this could be a fear-based scam aimed at coercing organizations into ransom payments for breaches that likely did not occur.
Ransomware attacks are increasingly targeting the healthcare industry, making it the third-most targeted sector behind finance and manufacturing. Reports indicate that these attacks surged by over 32% between 2023 and 2024. The threat extends beyond data loss as such incidents disrupt healthcare operations, hinder patient care, and create chaos for medical professionals.
A prominent example of the damage caused by cyberattacks is the Ascension cyberattack that took place in May 2024. This incident saw hackers lock medical personnel out of critical systems, disrupt communication lines, and obstruct the tools necessary for diagnosing and treating patients. Initially estimated to affect around 500 individuals, the impact later ballooned to nearly 5.6 million, emphasizing the serious repercussions of such breaches.
Additionally, the massive data breach experienced by UnitedHealth’s Change Healthcare unit in February 2024 further underscores the industry’s vulnerability. Initially reported to impact 100 million individuals, the figure eventually escalated to 190 million, marking it as the largest medical data breach in U.S. history. This alarming incident affected nearly half the population of the United States, with UnitedHealth attributing the attack to the ALPHV/BlackCat ransomware group, which claimed responsibility before law enforcement intervened.
In today’s landscape, organizations must take proactive measures to safeguard against ransomware threats. Implementing a robust cybersecurity framework is essential. Here are some essential strategies:
Healthcare organizations are notably lagging in adopting critical cybersecurity measures. The alarming reality is that many health institutions lack a Chief Information Security Officer (CISO) or a dedicated cybersecurity team. Often, these responsibilities fall to IT departments, which may lack specialized training. This oversight raises concerns, especially given the sensitivity of the data involved.
The prevalence of cyberattacks is set to increase, and without adequate defensive strategies, it only becomes a matter of time before more healthcare providers experience significant breaches. It is essential for the industry to prioritize the robust implementation of cybersecurity practices.
This situation prompts a crucial question: are current practices sufficient for safeguarding sensitive data? Moreover, how effectively is the government responding to capture those perpetrating these cybercrimes? As these discussions continue, the urgency for protective measures escalates.
For additional security insights and tips, consider subscribing to reliable sources focused on tech security. Stay informed, prioritize data protection, and take necessary precautions to defend against potential cyber threats.