Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
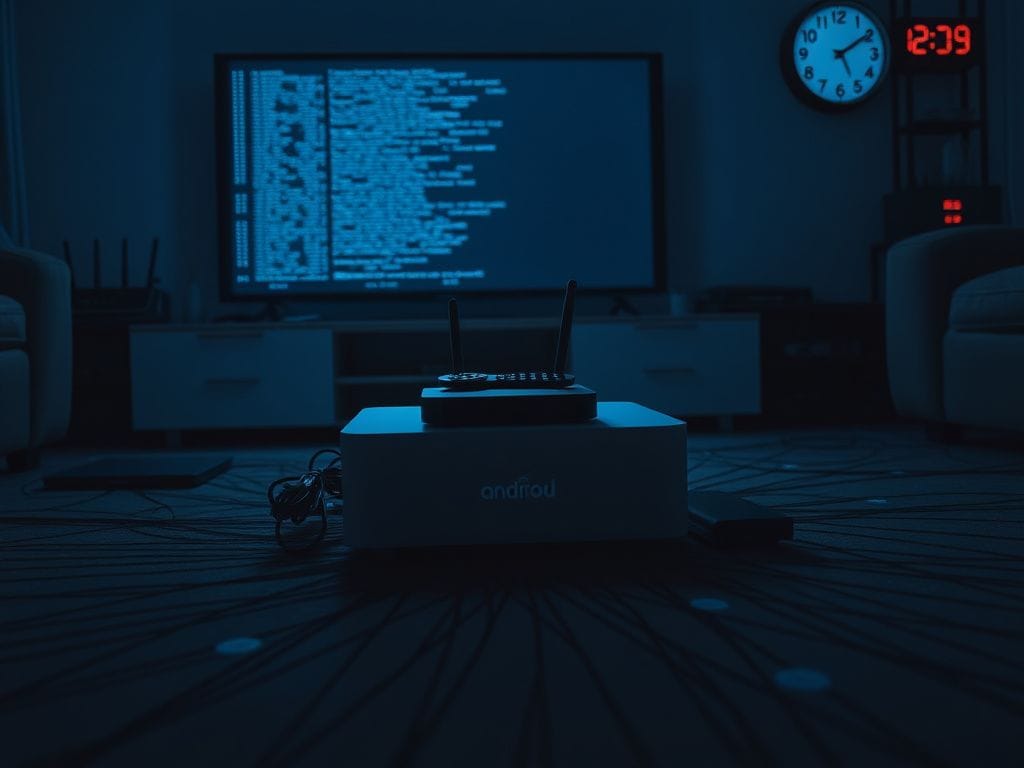
Android TV streaming boxes have surged in popularity, boasting promises of “everything for one price.” These devices are readily available on major retail platforms, featured in influencer videos, and recommended by friends who claim to have successfully cut the cord. While they appear appealing, security researchers caution that there may be hidden risks associated with these devices.
Reportedly, some Android TV boxes masquerade as simple media streamers but can actually transform your home network into a part of larger botnets, used for dubious online activities. Alarmingly, many consumers remain unaware of these risks.
Research from Krebs on Security reveals that certain media streaming devices do not function as ordinary streamers once connected to a home network. A specific examination of the SuperBox, an Android-based streaming box sold through various retailers, found significant concerns. SuperBox markets itself as a straightforward piece of hardware, asserting that it does not pre-install pirated applications and leaves responsibility for installations to users.
However, to access the extensive channel lineup advertised, users must first remove Google’s official app ecosystem and replace it with an unofficial app store. This crucial step should raise red flags for potential buyers. Following this installation, the device does more than stream content; it reroutes internet traffic through unverified third-party proxy networks, raising serious security concerns.
The implications of this rerouting are significant. Your home’s internet connection could be utilized for relaying traffic associated with ad fraud, credential stuffing, and extensive web scraping operations. During investigations conducted by Censys, researchers noted that SuperBox models connected to servers associated with Tencent’s QQ messaging service along with a residential proxy service named Grass.
Grass claims to be an opt-in network that allows users to earn rewards by sharing unused bandwidth, implying that SuperBox may employ software development kits or tools that hijack users’ bandwidth without explicit consent. This effectively turns the boxes into nodes within a larger proxy network.
In simpler terms, a botnet consists of a vast array of compromised devices that collaborate to manage traffic or execute online tasks without users’ awareness. Researchers uncovered that SuperBox devices harbored advanced networking and remote access tools not typically found in media-streaming devices. Examples of these tools include Tcpdump and Netcat, both of which are commonly utilized for network monitoring and traffic interception.
The devices also demonstrated capabilities for DNS hijacking and ARP poisoning within local networks, techniques aimed at redirecting traffic and impersonating other devices on the network. Some models even contained directories labeled