Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
ClickFix represents a sophisticated social engineering scheme that cybercriminals have increasingly utilized since early 2024 to propagate malware. This type of malware tricks users into executing harmful commands on their Windows PCs, and its prevalence is rising.
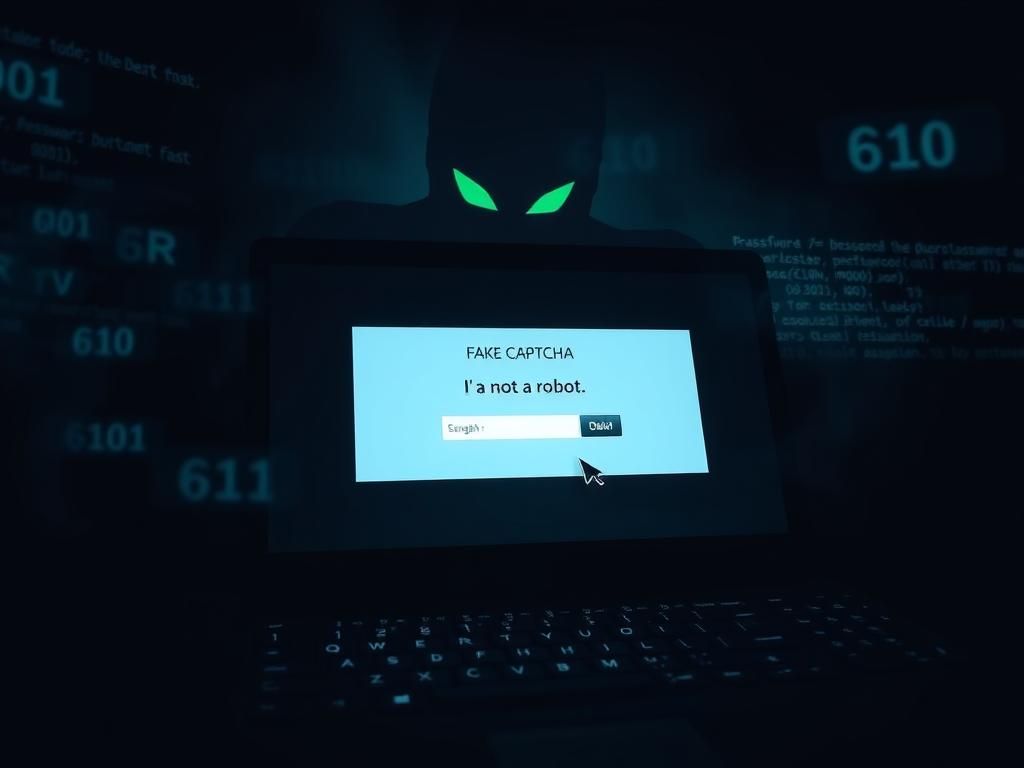
The fundamental lure is simple yet effective. Cybercriminals trick users into installing password-stealing malware while they believe they are merely confirming their humanity through a supposed CAPTCHA test. The use of keyboard shortcuts under the guise of bot verification reflects a troubling evolution in cybercrime.
Bots are computer programs designed to perform repetitive tasks online, often imitating human engagement. By manipulating users into adhering to these verification methods, hackers exploit the common lack of technological understanding, making individuals unwitting accomplices in their own malware infection.
According to insights from KrebsOnSecurity, the latest ClickFix operation ingeniously masquerades as a necessity for users to confirm their identity. Initially, targeted attacks focused on specific industries, but this tactic has now gained widespread traction, significantly impacting sectors like hospitality and healthcare.
The scheme typically initiates when a user visits a compromised or malicious website displaying a counterfeit CAPTCHA prompt. Once a user clicks the “I’m not a robot” button, they receive instructions to press a series of keyboard shortcuts. It starts with Windows + R, which opens the Windows Run dialog. Following that, pressing CTRL + V pastes a harmful script copied from the website’s clipboard. Hitting enter executes this script, resulting in the download and activation of malware.
The rise of ClickFix highlights a worrying trend wherein attackers leverage phishing emails and compromised websites to spread their harmful software. In particular, the hospitality sector has faced substantial threats, with scammers impersonating trusted platforms like Booking.com to distribute deceptive emails, enticing users to click links leading to ClickFix traps.
Healthcare workers also find themselves in the crosshairs, with malicious code integrated into popular physical therapy websites such as HEP2go. This broad targeting amplifies the risks associated with ClickFix malware.
Once ClickFix infiltrates a system, it can deploy various forms of malware, including password stealers like XWorm, Lumma Stealer, and DanaBot. These tools siphon login credentials and financial data, posing significant risks. Some iterations of ClickFix even deliver remote access trojans such as VenomRAT and AsyncRAT, granting hackers complete control over compromised systems. Furthermore, they may activate NetSupport RAT, which is frequently misused for cyber espionage.
Security experts have traced the origins of ClickFix back to March 2024. Reports indicated that attackers previously disguised themselves as fake error messages from applications like Google Chrome, Word, and OneDrive to lure unsuspecting users into downloading harmful files. The methods employed were strikingly similar, with victims prompted to click buttons that copied PowerShell commands, which they would inadvertently run in their systems.
The scope of ClickFix has broadened significantly by late 2024, with a notable focus on Google Meet users. Attackers would typically send emails with links to seemingly legitimate Google Meet sessions disguised as invitations from the victims’ organizations. However, upon clicking these links, victims were redirected to fake Google Meet pages displaying alarming messages about alleged issues with their systems.
Moreover, ClickFix has manifested through deceptive error pages on Chrome and fraudulent prompts for Facebook logins, further extending its reach across numerous platforms.
In response to the growing threat posed by ClickFix malware, users can adopt several key security measures to safeguard their devices and personal data. Implementing these practices can significantly reduce the risk of falling victim to such social engineering tactics.
1. Question CAPTCHA Prompts: Legitimate CAPTCHA tests do not require users to run commands, copy scripts, or paste them into PowerShell. If a site demands such actions, it is likely a scam. Users should exit the page immediately and refrain from further interaction.
2. Avoid Unverified Links and Enhance Antivirus Protection: Many ClickFix attacks initiate with phishing emails that mimic trusted services. Always verify the sender before clicking on any links. If an email appears urgent or suspicious, it’s safer to access the company’s official site directly rather than using links in the email.
The most effective defense against malicious links that can install malware is to employ robust antivirus software across all devices. High-quality software can also identify phishing emails and ransomware scams, ensuring the security of your personal information and digital assets.
3. Activate Two-Factor Authentication: Whenever possible, enable two-factor authentication. This extra layer of protection requires a secondary verification step, such as a code sent to your phone, in addition to your password.
4. Keep Devices Updated: Regular updates to operating systems, browsers, and security software are crucial in guarding against known vulnerabilities. Cybercriminals often exploit outdated systems, so enabling automatic updates serves as an effective protective measure.
5. Monitor Accounts and Change Passwords Regularly: If you suspect interaction with compromised sites or emails, check your accounts for unusual activity. This includes unexpected login attempts, unauthorized changes, or unknown transactions. If any anomalies arise, change your passwords immediately and notify the relevant services.
6. Invest in Personal Data Monitoring Services: Consider subscribing to services that keeps tabs on your personal information and provide alerts regarding potential breaches or unauthorized usage. While no service can guarantee total privacy, these services can help monitor and automate the removal of your information from various platforms.
ClickFix serves as a stark reminder that malware can often be deceptively simple. Cybercriminals have honed their techniques, rendering scams involving fake CAPTCHA prompts, phishing communications, and misleading pop-up messages more believable. The most effective strategy for online safety is continued vigilance. If a website requires you to undertake unusual actions, or if an urgent email requests immediate action, take a step back and verify before proceeding.
As technology continues to evolve, so too do the tactics of cybercriminals like those behind ClickFix. Staying informed about potential risks and being prepared to respond is key to maintaining your cybersecurity.